Latest news
- Removing the AUICGP instruction - Mar 23, 2026
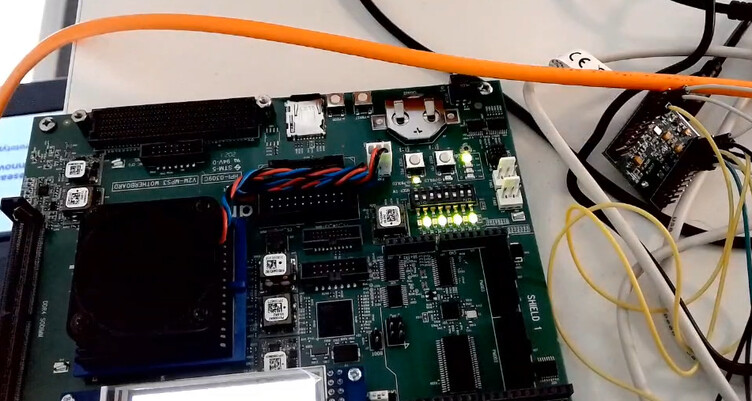
- First CHERIoT Silicon! - Mar 4, 2026
- CHERIoT vs the top 25 CWEs - Feb 4, 2026
- Post-Quantum Cryptography on CHERIoT - Dec 12, 2025
About
The Capability Hardware Extension to RISC-V for IoT (CHERIoT) platform was originally developed at Microsoft and is now part of an effort spanning multiple companies. It builds on top of CHERI to provide a solid foundation for secure embedded devices. CHERI provides referential integrity (pointers cannot be forged), spatial memory safety (pointers carry bounds that cannot be extended), call gates, and so on.
CHERIoT extends this with a complete platform providing deterministic use-after-free protection, a lightweight compartment model, lexically-scoped delegation of objects across compartment calls, and many more benefits.
The CHERIoT project comprises several repositories:
- The platform specification, including the formal model of the CHERIoT ISA. This is used to build an executable simulator and to prove properties of both the ISA and of implementations. The under-development (draft) version of the specification is built in CI. The 1.0 (current) release of the specification is also available.
- The CHERIoT RTOS, a clean-slate RTOS designed to take advantage of CHERIoT features. This provides the compartment model, a heap that can be safely shared across mutually distrusting compartments, and a host of other features.
- CHERIoT LLVM provides the toolchain for building the RTOS and other software that runs atop it.
- CHERIoT-Audit provides tooling for auditing the isolation properties of CHERIoT firmware images.
- The CHERIoT Ibex, an area-optimised core that implements the ISA. This is very slightly larger than the Ibex with a 16-element Physical Memory Protection unit, yet provides object-granularity memory safety and scales to a number of compartments bounded only by available memory.
- The CHERIoT small and fast FPGA emulator platform. This provides a set of peripherals such as a UART and interrupt controllers that provide a minimal useful integration of the Ibex.
The CHERIoT dev container includes the toolchain, the simulator built from the formal model, and a verilator simulation of the Ibex. This can be used explicitly via Docker / Podman or by opening the RTOS repository in Visual Studio Code or another editor that supports dev containers.
Getting started
It’s very easy to start developing for CHERIoT with either an Arty A7 or Sonata FPGA board, or with no hardware and using a simulator. The Sonata boards (which, unlike the A7, are designed specifically for prototyping CHERIoT-based systems) are now available to buy from Mouser.
The CHERIoT Getting Started Guide explains how to build and run code for all of these.
We also have a From zero to CHERIoT in two minutes with Sonata blog post hat explains how to start building and running code on Sonata in about the same amount of time as it will take you to get the board out of its box and plug it in.
Where to ask questions
We use GitHub Discussions for general queries about CHERIoT. This is persistent and searchable (without an account) and so a good place to ask questions that someone else may want to know the answer to.
We also have a public Signal chat. The Signal chat is intended for live discussions and automatically deletes messages. We encourage participants to write up the results of any discussions there in documentation, GitHub Discussions, Issues, or somewhere else that’s searchable. You can join the group from your phone by scanning this QR code:
